Design languages for design automation
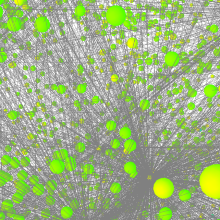
Graph-based design languages map terms (i.e. the "vocabulary") and assembly knowledge (i.e. the "rules") into recombineable language building blocks and operations. In the information representation of a design language, the nodes of a graph serve as abstract placeholders (i.e. as models) for real objects or processes. Thus a graph representation ("design graph") is machine-processed in place of the product design. This machine processing expands and modifies the graph dynamically at runtime by so-called "model-to-model transformations" (M2M). The abstract product representation allows a simple modularization and scalability and allows the consistent integration of different disciplinary domain models (see figure below). The coupling of the framework to domain-specific software systems is essential in order to integrate the existing knowledge and subprocesses. The couplings are implemented as interfaces that generate domain-specific models in the target format (DSL) from the abstract graph representation ("model-to-text transformations" (M2T)). There are already interfaces for geometry (CAD), multi-body systems (MBS), finite elements (FEM), flow analysis (CFD), etc. (see figure below).
Design analysis and evaluation
Using Buckingham's Pi theorem it is possible to transform a physical relationship of n dimensioned variables into a dimensionless description with only m = n - g dimensionless variables. Where g stands for the number of basic variables used. This knowledge can also be transferred to drafts - which can also be described by dimensioned variables - and reinterpreted as evaluation.
Every minimal description in the sense of the Pi theorem is an evaluation.
Digital factory
In addition to a multitude of boundary conditions, a product has a significant influence on the associated (digital) factory. The information already provided by a product created with graph-based design languages can be further processed automatically and used to generate suitable production sites. The aim is to be able to automatically design an optimal factory (in terms of costs, energy, time, etc.). This concerns the resources used as well as the manufacturing processes. In addition, the "Pi Group" is also concerned with the question of the optimal factory layout.
Automated cable routing and piping
Projects
The Center for Applied Research "Digital Product Lifecycle" (DiP) transfers the extremely powerful approaches of hardware and software development (e.g. the Unified Modellig Language UML) and adapts them to wide areas of mechanical engineering and automotive engineering. The aim is to integrate the entire product life cycle with all relevant product, process and resource-related data into a digital overall model and to provide the necessary processes, methods, tools and libraries.
The overall IDEaliSM aim can be divided into three main-objectives:
- An advanced integration framework for distributed multidisciplinary design and optimization enabling Competence Centres to offer and share engineering services and to collaborate in Distributed Development Teams.
- An Engineering Language Workbench: a set of domain specific and high-level modelling languages, ontologies and data standards to enable flexible configuration of engineering workflows and services and enable straightforward integration into distributed the advanced integration framework.
- A methodology for service-oriented development processes to redefine the product development process and information architecture to enable collaboration between service-oriented Competence Centers in Distributed Development Teams.
The resulting development framework will support European industries to enhance their level of integration and flexibility in product development to reduce the effort, cost and time-to-market in designing innovative aircraft and automotive structures and systems. As such, IDEaliSM fits well within the ‘Engineering Technology’ field identified in the ITEA2 research roadmap and the challenges within the Systems Engineering and Software Engineering domains.
Publications
Group members

Stephan Rudolph
PD Dr.-Ing.Head of research group "Design Theory and Similarity Mechanics"